MuddyWater GhostFetch CHAR MENA Targets

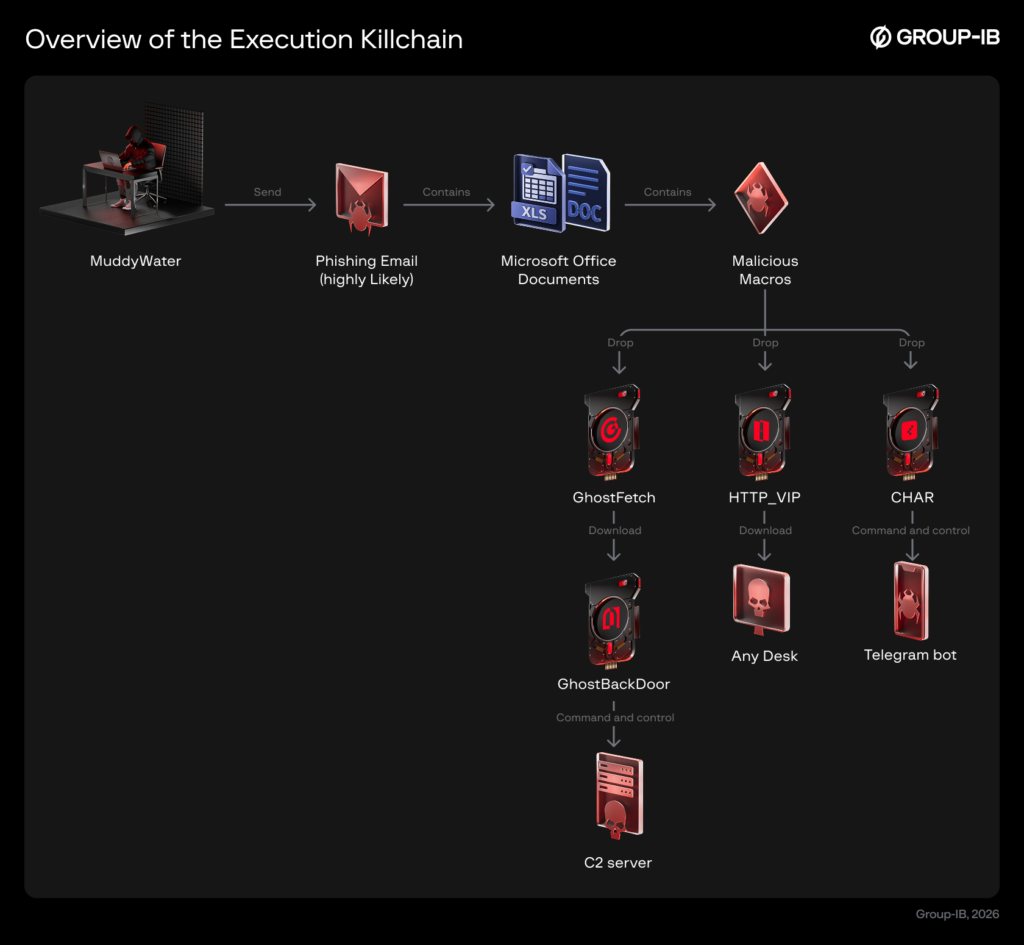
MuddyWater GhostFetch CHAR operations compromise MENA networks through phishing lures since January 26, 2026. Excel macros initiate chains deploying downloaders and implants, enabling remote control. Group-IB reports highlight Rust tools and AI-assisted code, risking data exfiltration and persistence.
MuddyWater Campaign Patterns
Attacks mimic MuddyWater tactics: phishing emails attach Office docs with macros decoding payloads for initial foothold. Variants use energy lures or flight tickets to evade detection. Observed overlaps confirm actor continuity across Earth Vetala aliases.
Operation Olalampo expands toolkit diversity for MENA focus.
GhostFetch Downloader Capabilities
GhostFetch performs reconnaissance on debuggers, VMs, AV, mouse activity, resolution before memory-executing secondaries. Leads to GhostBackDoor offering shell, file ops, re-execution. Evades analysis through environmental profiling.
MuddyWater GhostFetch CHAR tools enable stealthy persistence.
HTTP_VIP and AnyDesk Deployment
HTTP_VIP authenticates via codefusiontech[.]org, fetches AnyDesk for remote access. New variant adds shell, file transfer, clipboard capture, beacon updates. Themes disguise as reports/tickets for higher engagement.
Compromises integrity via unauthorized desktop control.
CHAR Rust Backdoor Features
CHAR leverages Telegram bot “stager_51_bot” for cmd/PowerShell execution. Deploys SOCKS5 proxies, Kalim backdoor, browser theft, sh.exe/gshdoc_release_X64_GUI.exe. Emojis in strings indicate AI coding aid, mirroring BlackBeard/Archer RAT structure.
Telegram C2 diversifies evasion from traditional infra.
AI in Malware Development
Source code artifacts align with Google’s prior findings on MuddyWater AI use for custom tools. Shared Rust env with BlackBeard targets Middle East entities. Public server exploits supplement phishing for access.
MuddyWater GhostFetch CHAR evolutions incorporate AI tooling.
MuddyWater persists in META via diversified C2, custom Rust malware, server vulns. Phishing disrupts availability through backdoor control; browser exfil hits confidentiality. Group-IB analysis details defenses against ongoing regional threats.







No Comment! Be the first one.