CVE-2026-20079 Cisco FMC RCE Exploit Details

A critical flaw tracked as CVE-2026-20079 Cisco exposes Secure Firewall Management Center systems to remote attacks. The issue allows attackers to bypass login and execute commands. This matters because many exposed systems sit on public networks. As a result, attackers can target organizations that rely on these devices for network security.
Researchers found that the bug appears during system startup. When the device boots, it creates a session that stays active if no user logs in. However, attackers can reuse this session and turn it into a valid login session. This behavior creates a dangerous window where unauthorized access becomes possible without any credentials.
CVE-2026-20079 attack method explained
Attackers begin by using a fixed session ID created during boot. Next, they log in using hardcoded credentials tied to system accounts. As a result, they upgrade the session into a valid web interface session. This step gives them limited access, but it is enough to continue the attack.
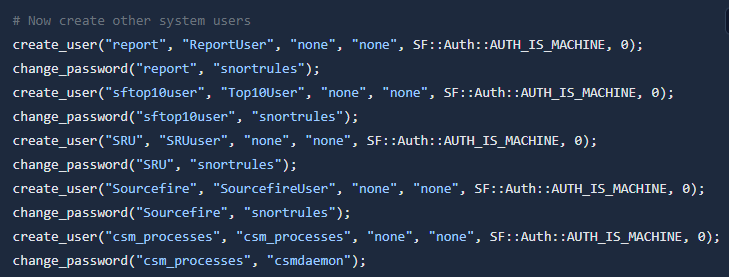
Meanwhile, the system fails to properly verify user type. This allows attackers to access internal APIs with limited checks. After that, they extract a required token and move deeper into the system. Then, attackers use API endpoints to write a malicious script to the device. They trigger another function that executes the script. Finally, the system runs the script with root privileges, giving full control over the device.
Impact and exposed systems
The flaw carries a CVSS score of 10.0, which signals maximum severity. Also, scans show hundreds of exposed systems online, increasing the risk of real attacks. Because these devices manage firewall operations, a successful attack can disrupt entire networks.
However, exploitation depends on timing. The vulnerable session exists mainly after a reboot. If users interact with the system, it may remove the session and block the attack. Even so, unattended or rarely used systems remain at high risk. Attackers can gain full access, run commands, and control firewall operations without detection.
Response and what comes next
Cisco released a security advisory and provided patches to fix the issue. Organizations should update affected systems immediately to block exploitation. In addition, admins should restrict public access to management interfaces. This reduces the chances of attackers reaching vulnerable systems.
Monitoring login activity and reboot events can also help detect suspicious behavior. For example, unusual session activity after a reboot may signal an attack attempt. Finally, CVE-2026-20079 highlights how small session handling flaws can lead to major breaches. Attackers continue to target network devices, so timely patching and strong access controls remain essential.






[…] critical-severity vulnerability in Smart Software Manager On-Prem (SSM On-Prem) product that could allow an unauthenticated, remote attacker to execute arbitrary […]