Microsoft Confirms RDP Dialog Rendering Bug in April 2026 Update
Microsoft has officially confirmed a known issue in its April 2026 Windows 11 cumulative update, where Remote Desktop Protocol (RDP) security warning dialogs render incorrectly on certain system configurations, a critical usability flaw, given that these warnings are specifically designed to protect users from active phishing threats.
The bug was introduced alongside the April 14, 2026, Patch Tuesday security update, affecting KB5083769 for Windows 11 versions 25H2 and 24H2, and KB5083768 for Windows 11 version 26H1.
Both updates delivered new RDP security warnings as part of Microsoft’s broader initiative to combat CVE-2026-26151, a Remote Desktop spoofing vulnerability that had been actively exploited in the wild.
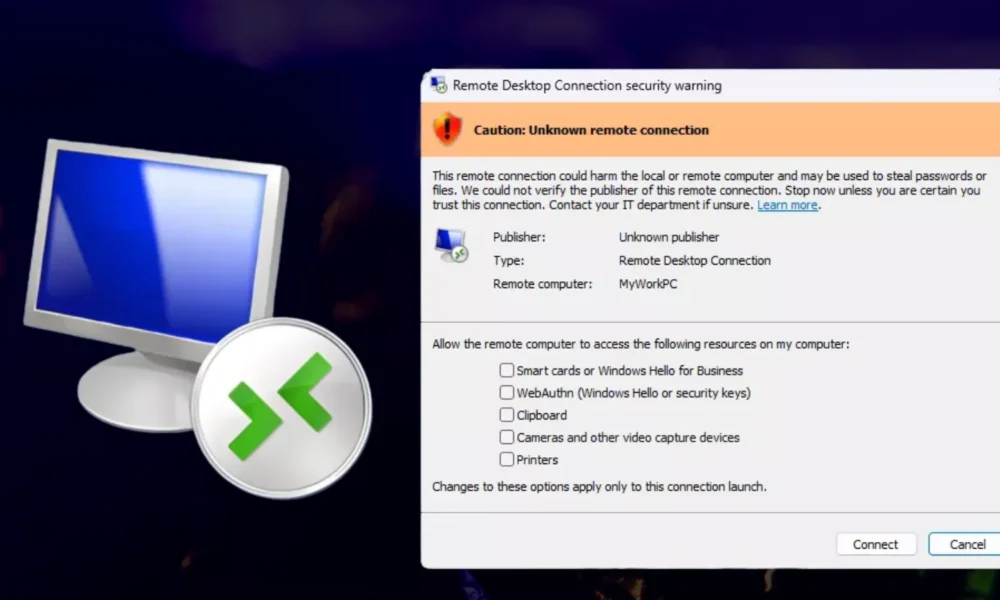
The newly introduced warning dialog was engineered to display a clear, detailed prompt before any RDP connection is established.
It is intended to show the publisher verification status, the remote computer’s address, and available local resource access options, providing users with a meaningful trust checkpoint before granting a remote machine access to sensitive local resources such as clipboards, smart cards, printers, and cameras.
Remote Desktop Warnings Incorrect
Users quickly began reporting failures with the new dialog after deployment. Microsoft formally added the issue to its known issues list on April 23, 2026, and issued a correction to its documentation on April 27, 2026.
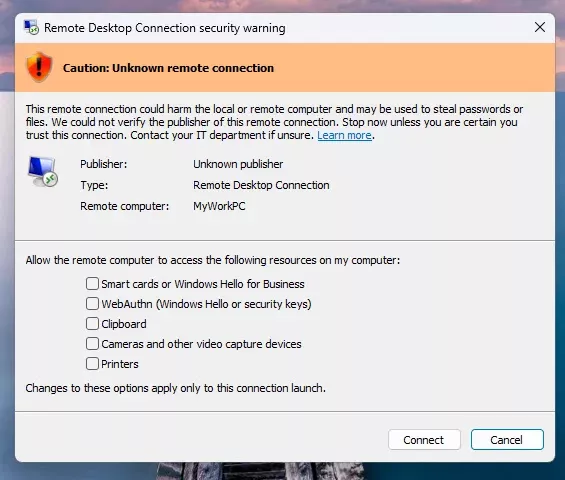
According to Microsoft’s support documentation, the rendering failure specifically manifests on multi-monitor systems with mismatched display scaling settings.
For instance, if one monitor is configured at 100% scaling and a second at 125%, the RDP warning window may render with overlapping text or partially hidden buttons, making the security prompt difficult or impossible to read and interact with.
This is particularly concerning because the dialog serves as the primary trust gate that users must clear before any RDP session proceeds. An unreadable or obscured warning effectively undermines the entire security control.
The April 2026 RDP warnings were introduced to counter weaponized .rdp file-based phishing campaigns, where threat actors distribute malicious RDP configuration files to silently hijack credentials or redirect sensitive local resources to attacker-controlled infrastructure.
The same updates also turned off local resource redirection by default for pre-configured RDP files, requiring explicit user acknowledgment on each new connection, a significant behavioral change for enterprise environments.
Microsoft has indicated a permanent fix will be delivered in a future cumulative update. In the interim, enterprise administrators are strongly advised to monitor mixed-DPI workstations closely, particularly those operating across multiple monitors with differing scaling configurations, to ensure security prompts.




No Comment! Be the first one.