GhostLock Attack Locks 500K Files Without Encrypting Any Data

A newly disclosed proof-of-concept GhostLock attack is challenging one of the most fundamental assumptions in enterprise ransomware defense that destructive file system attacks require data encryption.
Published in May 2026 by security researcher Kim Dvash, the open-source tool demonstrates how a standard low-privileged domain user account can lock hundreds of thousands of files across enterprise network-attached storage, triggering catastrophic operational disruption without writing a single corrupted byte to disk.
The attack’s core mechanism doesn’t exploit an obscure zero-day vulnerability. Instead, it abuses the fully documented CreateFileW API, a standard Windows operating system function.
GhostLock Attack Locks 500K Files
When a network client calls this API with the sharing mode parameter explicitly set to zero, the I/O manager grants an exclusive deny-share handle to the requesting process.
Under the Server Message Block (SMB) protocol specification, the receiving server is required to enforce this share contract meaning no other process or user can read, write, or delete the targeted file until the malicious actor voluntarily closes the handle.
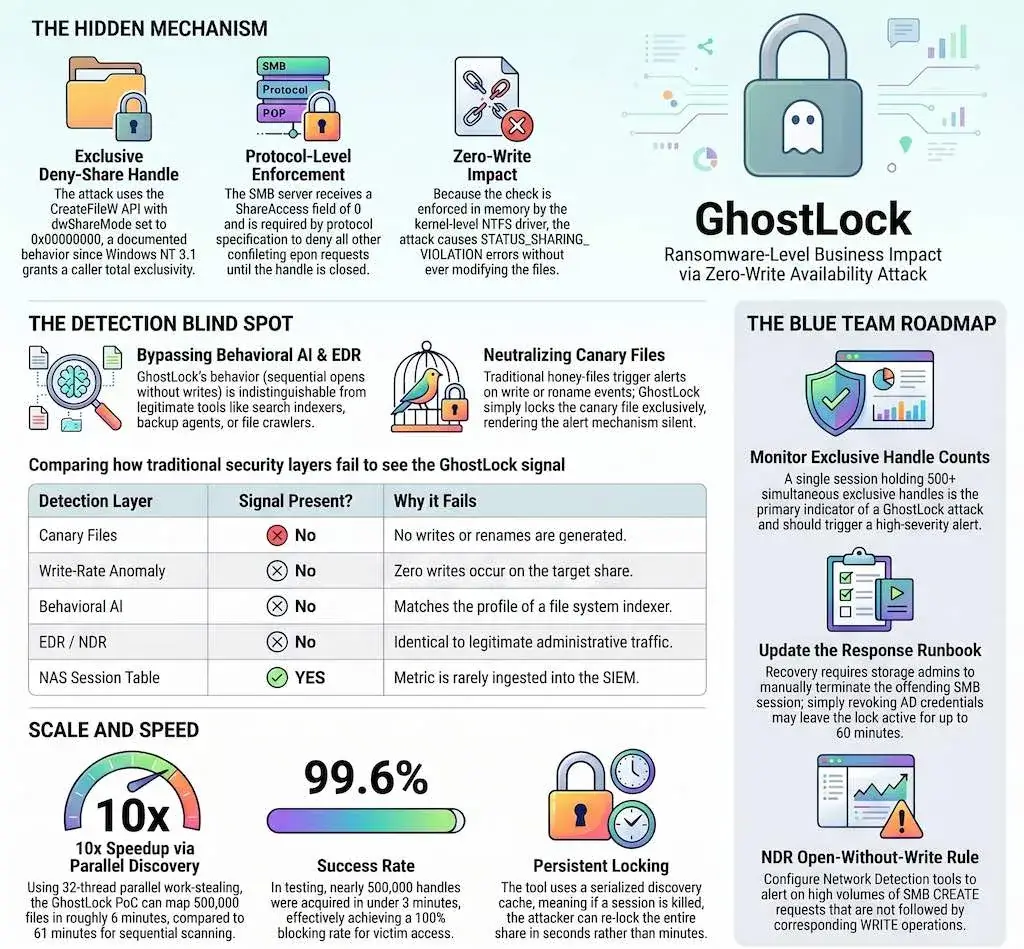
Critically, the file system driver enforces these sharing semantics entirely in memory at the kernel level, leaving no user-mode bypass available.
GhostLock weaponizes this standard behavior at enterprise scale through a highly optimized, multithreaded parallel discovery architecture.
By simultaneously scanning directories and requesting exclusive read-only handles across multiple threads, the automated script can locate and lock approximately 500,000 files on a corporate network share in under three minutes, according to analysis by Andrea Fortuna.
The most alarming aspect of GhostLock is its ability to bypass nearly every layer of modern cybersecurity architecture simultaneously.
Security honeypots and canary file strategies are rendered useless because the attack generates zero write, rename, or delete events on the compromised storage volume.
Behavioral AI models and write-rate anomaly detectors fail to trigger because the network traffic profile is virtually indistinguishable from a legitimate enterprise search indexer or routine backup application opening documents in rapid succession.
At the endpoint detection and response (EDR) level, the system calls appear identical to a standard employee rapidly opening Office documents, producing no shellcode injections or memory anomalies.
Data loss prevention (DLP) tools remain completely silent as well, since the attacker opens files without actively exfiltrating their contents, keeping outbound network traffic well below established alerting thresholds, as reported by Andrea Fortuna.
Because restricting the underlying CreateFileW API would break legitimate enterprise software operations, security operations centers must pivot to specialized telemetry-based detection.
The single reliable indicator of a GhostLock attack resides within the storage management session table, which tracks simultaneous exclusive handles per user session.
Security teams should ingest this telemetry into their SIEM platforms and configure critical alerts for any single session exceeding 500 exclusive file handles.
Incident response teams must also update their runbooks immediately. Standard forensic investigations will find no modified timestamps or new files, frequently misdirecting analysts.
Critically, simply revoking the compromised Active Directory credentials is insufficient the pre-authenticated SMB session will maintain its file locks until connection timeout.
Effective containment requires direct coordination with storage administrators to forcefully terminate the offending network session at the storage infrastructure layer.
The GhostLock disclosure highlights an urgent gap in how enterprises define and monitor for ransomware-style attacks, demanding a fundamental reassessment of what constitutes a file system lockout threat.







No Comment! Be the first one.