DarkSword Goes Global as New iOS Zero-Day Chain Hits Multiple Targets

A newly uncovered iOS exploit chain dubbed DarkSword is rapidly proliferating across multiple threat actors, enabling full device compromise through a sophisticated multi-stage attack. First observed in November 2025, the chain leverages six zero-day vulnerabilities to achieve remote code execution, sandbox escape, and kernel-level privilege escalation on iOS devices running versions 18.4 to 18.7 .
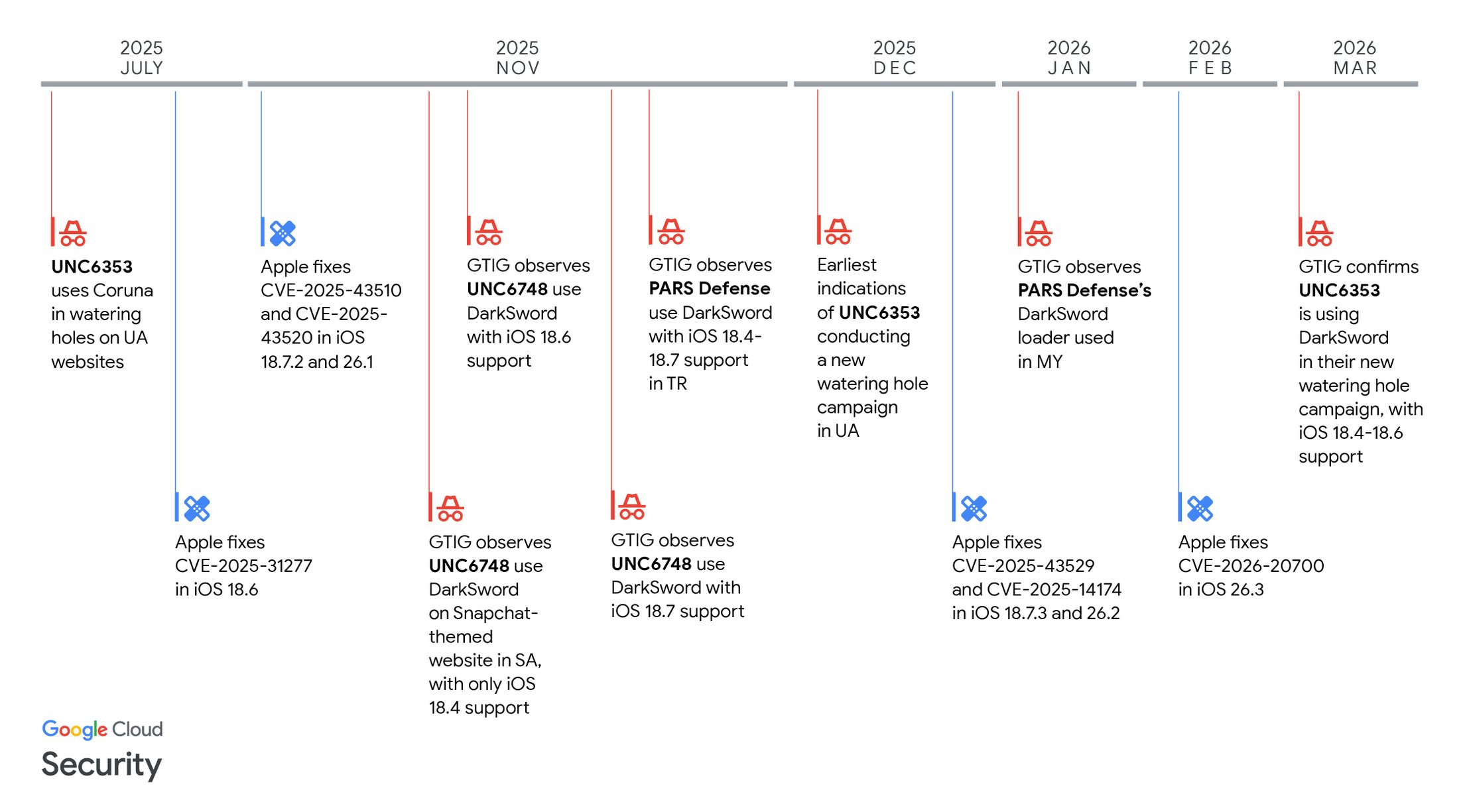
Figure 1: Timeline of DarkSword observations and vulnerability patches
Unlike traditional exploit kits, DarkSword is entirely JavaScript-based, eliminating the need for native binaries and allowing attackers to bypass key iOS protections such as PPL and SPTM. This design significantly lowers operational complexity while maintaining high effectiveness .
Infection Chain Overview
| Stage | Component | Vulnerability | Purpose |
|---|---|---|---|
| Initial Access | Malicious website / watering hole | — | Victim redirection & exploit delivery |
| RCE | JavaScriptCore exploits | CVE-2025-31277, CVE-2025-43529 | Arbitrary code execution |
| PAC Bypass | dyld flaw | CVE-2026-20700 | Bypass pointer authentication |
| Sandbox Escape 1 | WebContent → GPU | CVE-2025-14174 | Escape browser sandbox |
| Sandbox Escape 2 | GPU → system process | CVE-2025-43510 | Expand privileges |
| Privilege Escalation | Kernel exploit | CVE-2025-43520 | Full device compromise |
Multi-Actor Adoption
DarkSword’s most alarming trait is its rapid adoption by multiple actors, including surveillance vendors and suspected state-linked groups. Campaigns targeted users in Saudi Arabia, Turkey, Malaysia, and Ukraine using tailored delivery methods such as:
- Fake Snapchat-themed sites with obfuscated JavaScript loaders
- Watering hole attacks injecting malicious scripts into legitimate websites
- Encrypted exploit loaders using ECDH + AES for stealth delivery
Each actor modified the base framework, adding anti-debugging, device fingerprinting, or improved exploit selection logic.
Post-Exploitation Malware
DarkSword deploys three main payload families:
| Malware | Capability Highlights |
|---|---|
| GHOSTKNIFE | Full-featured spyware (messages, mic, screenshots, files) |
| GHOSTSABER | Modular backdoor with command execution & data exfiltration |
| GHOSTBLADE | Data harvester targeting communications, credentials, and location |
Notably, GHOSTKNIFE uses encrypted C2 communication and actively deletes crash logs to evade detection , while GHOSTBLADE focuses on bulk data theft including iMessage, WhatsApp, Wi-Fi credentials, and even cryptocurrency wallet data .
Key Takeaways
DarkSword highlights a growing trend: exploit commoditization. A single advanced exploit chain is now reused and adapted by multiple actors, mirroring earlier kits like Coruna. This lowers the barrier to entry for high-end surveillance operations and increases global risk exposure.
All vulnerabilities have been patched in recent iOS updates, and users are strongly advised to update devices immediately or enable Lockdown Mode where updates are not possible.





No Comment! Be the first one.