Infostealer.Speagle Hijacks Cobra DocGuard Software

A sophisticated new malware threat is currently weaponizing legitimate security infrastructure to perform industrial espionage. Cybercriminals developed Infostealer.Speagle to inhabit the ecosystem of Cobra DocGuard, a popular document encryption platform.
This parasitic approach allows the malware to mask its data theft as routine communication between the software and its server. Consequently, traditional network monitoring tools may fail to flag the exfiltration of highly sensitive documents.
The core technical problem lies in how Infostealer.Speagle hijacks the trusted environment of the host software. It specifically hunts for computers with Cobra DocGuard installed to ensure its malicious traffic blends in perfectly.
Furthermore, the malware uses legitimate device drivers to perform self-deletion, effectively erasing its footprints after the theft. This level of technical trickery makes detection incredibly difficult for organizations relying solely on standard signature-based antivirus.
However, the solution starts with identifying the specific behavioral patterns of this threat. Security teams must monitor for unauthorized registry queries involving Esafenet paths and unusual WMI activity. In addition, organizations should implement strict egress filtering to flag any HTTP POST requests using the “Raw HTML Reader” user agent. Furthermore, isolating critical systems from the broader document management infrastructure can limit the reach of Infostealer.Speagle.
Hunting for Ballistic Missile Intelligence
This malware is not a generic threat; it targets specific high-value intelligence. One variant of Infostealer.Speagle contains a hardcoded list of keywords related to Chinese ballistic missiles and hypersonic technology.
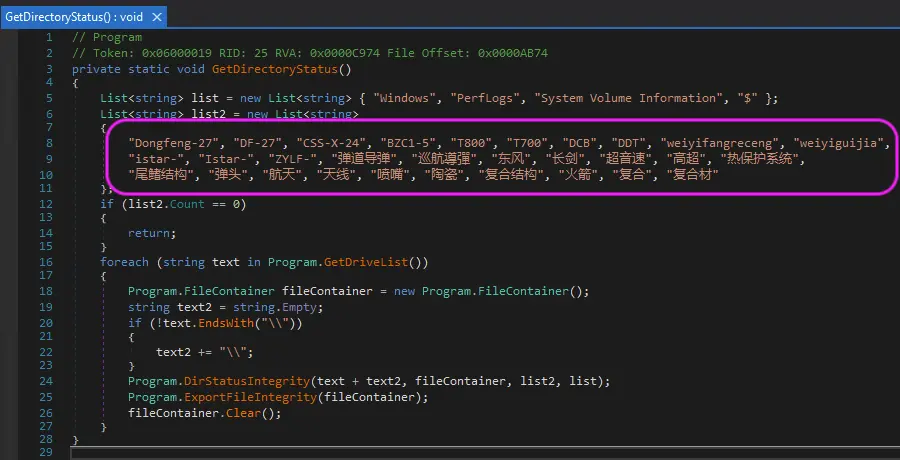
It systematically scrapes directories for terms like “Dongfeng-27” and “thermal protection system.” Consequently, this suggests the involvement of a state-sponsored actor or a specialized private contractor.
The malware also performs deep browser harvesting to steal session tokens and login data. It targets SQLite databases associated with web history and autofill information to expand its reach. Furthermore, it utilizes a multi-phase exfiltration strategy to ensure it captures at least partial data if the process is interrupted. Consequently, the Infostealer.Speagle threat represents a high-velocity risk to aerospace and defense sectors.
Strengthening Supply Chain Resilience
Defending against such a targeted threat requires a move toward total supply chain transparency. You must verify the integrity of all security software updates and monitor for tampered drivers. Furthermore, adopting a zero-trust model for internal servers can prevent hijacked infrastructure from communicating with infected endpoints. By staying alert to these parasitic methods, you can secure your most sensitive data.





No Comment! Be the first one.