OpenClaw Exploitation Multiple Threat Groups

Rapid adoption of OpenClaw AI assistant framework exposes enterprises to OpenClaw exploitation, with over 312,000 instances vulnerable on default port 18789. Flare analysis reveals attacks starting 72 hours post-viral spread in late January 2026, using RCE (CVE-2026-25253), supply chain compromises, and credential grabs. Design granting system privileges and persistent memory amplifies risks to confidentiality and network integrity.
Scale of OpenClaw Exploitation
Scans identify 312,551 Linux/OpenClaw exposures, concentrated in China (62,790), US (59,571), Israel (41,736), Singapore (23,542), UK (20,223). Default configs bind interfaces publicly without auth, enabling unauthenticated admin access and reverse proxy bypasses. Honeypots confirm exploits within minutes, harvesting API keys, OAuth tokens, and passwords via Telegram-shared malware.
Persistent memory facilitates long-term surveillance, eroding data availability in integrated messaging.

ClawHavoc Supply Chain Campaign
Campaigns like ClawHavoc, detected January 29, 2026, masquerade as crypto tools (“solana-wallet-tracker”) with curl-based installers deploying Atomic Stealer (Mac) or keyloggers (Windows). CVE-2026-25253 (CVSS 8.8) enables RCE across pre-2026.1.29 versions, compromising user privileges for lateral movement in enterprises.
The table below specifies the core OpenClaw exploitation vulnerability.
| CVE Identifier | Vulnerability Description | CVSS Score |
|---|---|---|
| CVE-2026-25253 | Remote code execution vulnerabilities | 8.8 |
This table outlines the high-severity RCE flaw driving compromises.
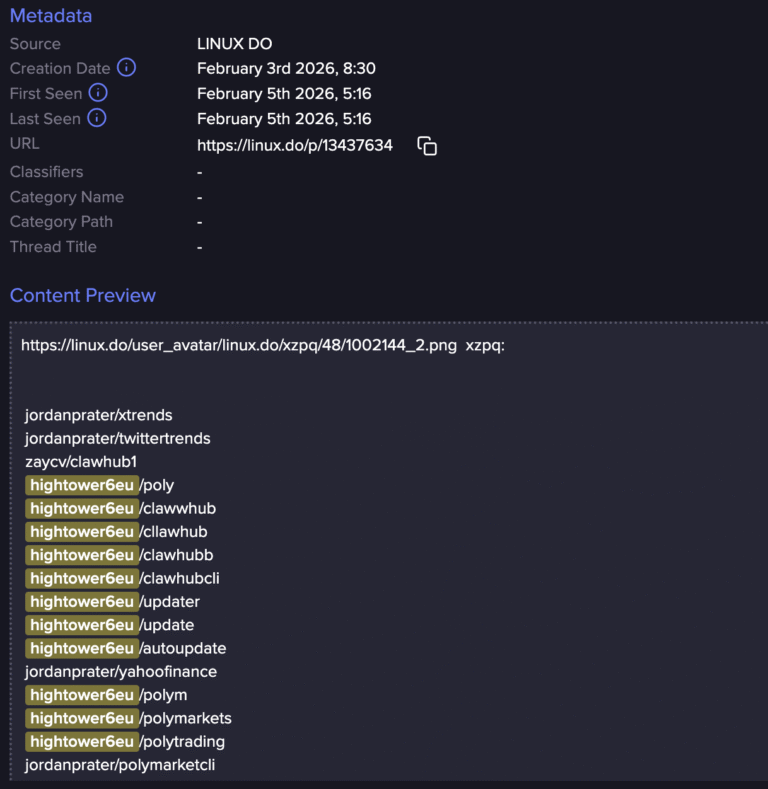
ClawHub Skill Poisoning Attacks
ClawHub marketplace, lacking scans or reviews, hosts impersonated skills from aged GitHub accounts since February 1. “Hightower6eu” variants automate mass deployments with malicious “Prerequisites” executing shells or webhooks for exfiltration. Trust model enables account takeovers, distributing stealers across OpenClaw users.
Supply chain integrity falters, injecting payloads into autonomous workflows.
Threat Actor Targeting Patterns
OpenClaw exploitation signals shift to AI agents, with groups honing RCE, poisoning, and interface exposures. Organized efforts indicate criminal and state monitoring of viral tools. Creator Peter Steinberger’s security deprioritization comments underscore design flaws now at OpenAI.
Architectural autonomy trades capability for controls, aligning with actor goals for persistence.
Implications for AI Agent Deployments
Security teams confront exfiltration via privileged access and skills ecosystem. Enterprise rollouts risk footholds; strategic shifts demand security-by-design in agents. Flare vows ongoing tracking of criminal/nation-state activity amid expanding exposures.
OpenClaw exploitation campaigns evolve rapidly, demanding config hardening and marketplace oversight.
OpenClaw exploitation campaigns compromise agent integrity, enabling credential drains and persistence that disrupt operations and confidentiality. Post-2026.1.29 patches, local binding, and ClawHub vetting counter vectors per researcher advisories. Deployment caution preserves AI workflow availability against opportunistic threats.







[…] Vulnerabilities: Devices with outdated software or insecure configurations may become entry points for cyberattacks. […]