TheGentlemen ransomware exposed open server leak

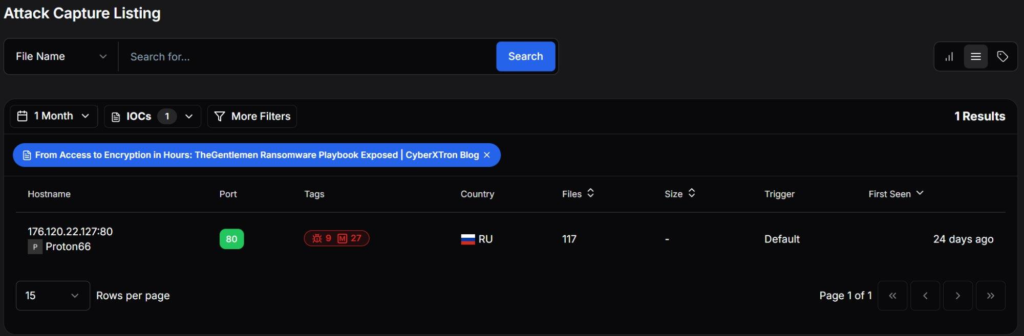
A major security lapse has revealed how the TheGentlemen ransomware group operates in real attacks. An open server hosted on Proton66 exposed a full toolkit along with real victim data. The leak shows how attacks were carried out and why this matters for organizations worldwide.
TheGentlemen ransomware exposed toolkit online
Investigators found a public directory filled with files tied to TheGentlemen ransomware exposed activity. Instead of random files, the attackers arranged everything in a clean structure. Each folder served a clear purpose in the attack process.
For example, some tools handled scanning, while others focused on gaining access or turning off security. As a result, the setup looked like a ready-to-use attack kit rather than stored malware.
Attack tools show full intrusion process
The exposed files clearly show how attackers move inside a system step by step. First, they scan networks. Then, they gain higher access. After that, they disable security before launching ransomware.
Key actions included:
- Stealing credentials using Mimikatz
- Shutting down security tools across systems
- Creating remote access using tunnels
- Running scripts to prepare systems for attack
Because of this setup, attackers can run most actions quickly using a single script.
TheGentlemen ransomware exposed real victim data
More importantly, the directory contained real stolen data. Logs showed usernames, password hashes, and activity from earlier attacks. This proves the tools were already used in real environments.
In addition, exposed authentication tokens could help track attacker activity on other systems. TheGentlemen ransomware exposed operations show that attackers rely on common tools, which makes detection harder for many organizations.
Open server leak raises security concerns
This open server gives a rare look into how ransomware attacks work from start to finish. At the same time, it shows how a small mistake can expose a full operation.
Security teams should watch for warning signs such as:
- Sudden shutdown of security tools
- Credential dumping activity
- Unexpected remote access connections
- Multiple services stopping at once
Overall, TheGentlemen ransomware exposed case shows that even skilled attackers can slip up, and those mistakes can reveal everything.





No Comment! Be the first one.