MS SQL Server Attacks Deploy ICE Cloud Malware

A threat actor tracked as Larva-26002 continues to target exposed MS-SQL servers. These systems often rely on weak credentials, making them vulnerable to brute force and dictionary attacks.
Once access is gained, attackers quickly move to system reconnaissance. Commands such as hostname, whoami, and netstat help map the infected environment.
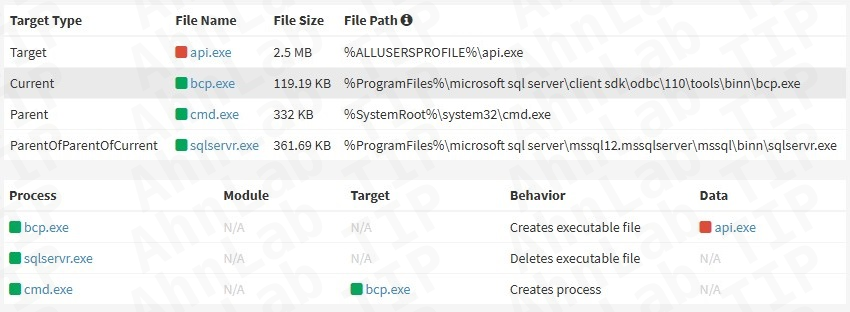
MS SQL Server Attacks exploit BCP utility
Attackers abuse the Bulk Copy Program utility to deploy malware. They store malicious binaries inside database tables and export them as executable files.
Consistent identifiers such as uGnzBdZbsi and FODsOZKgAU.txt appear across campaigns. This pattern links current operations with earlier ransomware-based attacks.
ICE Cloud malware introduces new capabilities
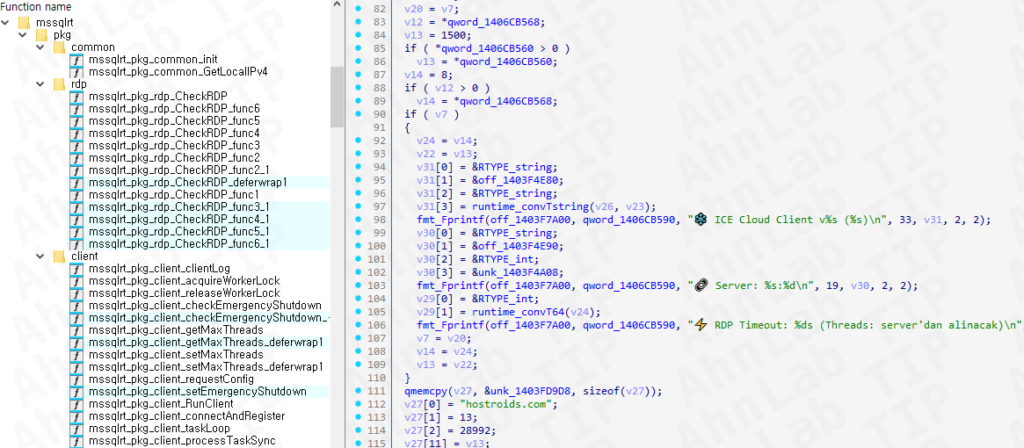
The deployed payload installs ICE Cloud Client, a scanner written in Go. This malware acts as both a brute-force tool and a scanning engine for further targets.
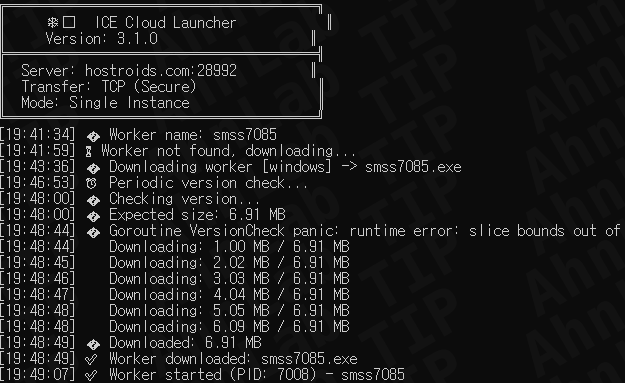
The binary includes Turkish language strings and uses randomized filenames. These traits suggest continuity with earlier Mimic ransomware operations.
Flexible attack delivery methods observed
Attackers adapt when BCP execution is restricted. They use Curl, Bitsadmin, and PowerShell to download payloads directly from remote servers.
This flexibility allows continued infection even in partially secured environments. It also increases the likelihood of successful deployment across varied configurations.
Command and control driven scanning
The ICE Cloud Client communicates with a remote server for instructions. It receives lists of target systems along with default credentials for authentication attempts.
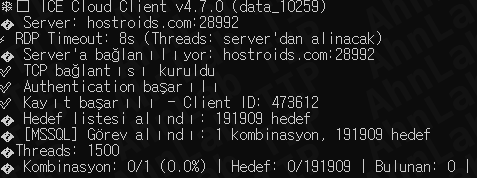
The malware reports successful logins back to the control server. This enables automated expansion of attacks across multiple exposed databases.
Security implications for organizations
MS SQL Server Attacks present serious risks for enterprises relying on legacy configurations. Unsecured database servers can become entry points for broader network compromise.
Repeated infections occur when access controls and password policies remain weak. Organizations must enforce strong credentials and restrict public exposure of database services.
Outlook on evolving attack patterns
Attackers continue refining techniques to maintain persistence. The shift from ransomware to scanning tools highlights a broader targeting strategy.
MS SQL Server Attacks will likely increase as exposed systems remain online without proper safeguards.
Organizations that delay updates and monitoring face a growing risk of compromise.






No Comment! Be the first one.