DEEP#DOOR Malware Steals Credentials via Python Backdoor

A newly identified Python-based DEEP#DOOR malware has emerged as a serious threat to Windows environments, deploying a fully-featured remote access backdoor alongside a broad credential-harvesting engine capable of exposing an entire organization’s access surface in a single infection.
Securonix Threat Research analysts first identified and documented the DEEP#DOOR framework, describing it as an obfuscated batch loader designed to deploy a persistence and credential-stealing implant on Windows systems.
The infection begins when a user executes what appears to be a routine batch script, typically named “finallyJob.bat”, on a Windows machine.
Unlike conventional malware that fetches external payloads post-infection, DEEP#DOOR takes a self-contained approach to the full Python Remote Access Tool payload (c.py) is embedded directly within the batch file itself.
This design significantly reduces the likelihood that network-based detection tools will intercept the threat before it fully takes hold.
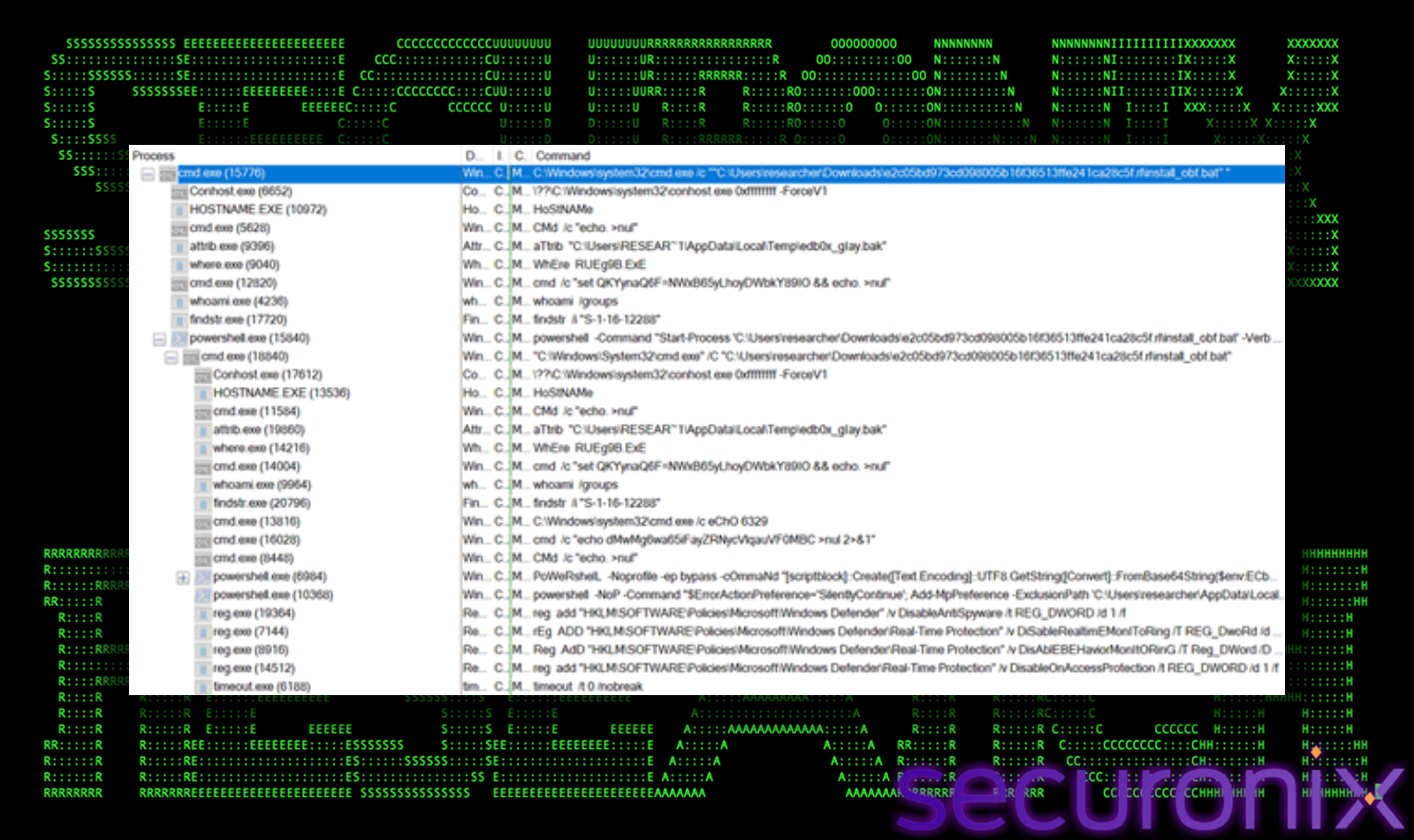
Once triggered, the batch script dynamically extracts and executes the embedded Python RAT, then establishes persistence through multiple redundant mechanisms: Startup folder scripts, Registry Run keys, Scheduled Tasks, and optional WMI subscriptions.
Before deploying its core implant, DEEP#DOOR aggressively dismantles host-based defenses. The malware disables Windows SmartScreen, patches both AMSI and ETW to bypass security tooling, clears event logs, and applies timestamp-stomping to conceal file activity from forensic review.
Additional evasion techniques include sandbox detection, API unhooking, tampering with Windows Defender, and stripping command-line arguments. These layered techniques make DEEP#DOOR exceptionally difficult to detect using traditional signature-based antivirus solutions.
Once active, the implant communicates with attacker-controlled infrastructure through a publicly available TCP tunneling service, enabling remote operators to issue commands over dedicated ports.
Surveillance capabilities include keylogging, webcam photo capture, microphone recording, and full-screen capture, establishing long-term persistence and enabling post-exploitation lateral movement.
The most damaging component of DEEP#DOOR is its systematic credential-harvesting engine, which targets multiple credential stores simultaneously:
- Browser credentials —
get_chrome_cred()andget_edge_cred()functions access browser SQLite databases to extract stored login data from Chrome and Edge - SSH private keys —
get_ssh_key()discovers and exfiltrates private keys used for remote server access - Cloud authentication tokens —
get_cloud_cred()scans configuration files and environment variables for AWS, Azure, and GCP credentials - Wi-Fi passwords —
get_wifi_cred()queries the Windows Credential Manager and related registry locations for saved wireless credentials
This multi-vector collection means a single compromise can expose an organization’s entire access surface at once.
Even after the malware is removed from the original host, according to Securonix, attackers retain harvested credentials for persistent re-entry.
Mitigation
Security teams should take the following steps to reduce exposure:
- Avoid opening unknown batch files or script attachments received via email or shared links
- Monitor for unusual PowerShell and
cmd.exeactivity combined with Base64-encoded commands - Audit Registry Run keys, Startup folders, and Scheduled Tasks regularly for unauthorized entries
- Enable Windows Defender tamper protection to block in-memory defense disabling
- Rotate cloud authentication tokens and SSH keys immediately following any suspected compromise
Because DEEP#DOOR relies on Python-based execution and obfuscated scripting rather than compiled binaries, traditional antivirus solutions may offer limited coverage. Behavioral analytics and anomaly detection should serve as the primary defense layer for organizations facing this class of evolving threat.






No Comment! Be the first one.