Magento PolyShell vulnerability enables file upload RCE

The Magento PolyShell vulnerability exposes thousands of online stores to serious risk. Attackers can upload malicious files without login and gain control in some cases. This matters because many businesses rely on Magento for daily sales and customer data.
Magento PolyShell vulnerability enables attack path
Attackers use a public API to upload files through shopping cart features. First, they create a cart and fetch a product ID. Then, they send a crafted request with hidden file data.
However, the system only checks if the file looks like an image. It does not verify the file extension properly. As a result, attackers can upload disguised malicious files.
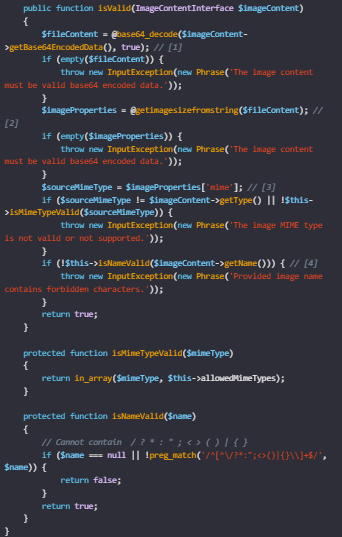
Attackers bypass checks with simple tricks
Attackers hide code inside image files to bypass validation checks. For example, they add malicious code into image metadata or use simple file tricks. Meanwhile, the system accepts the file as valid.
Next, the file gets stored on the server with attacker-controlled names. Because of this, attackers can later access or run the file under certain conditions.
Magento PolyShell vulnerability exposes sites to risk
The impact depends on server setup, but risks remain serious. In some cases, attackers can run code and take control of the system. In other cases, they may still store harmful files for later use.
In addition, future server changes can make these files dangerous even if they seem safe now. Magento PolyShell vulnerability highlights how small validation gaps can lead to major security issues.
Fixes pending as users must take precautions
Magento has not yet released a full patch for stable versions. However, newer versions include partial fixes that block risky file types. Until then, site owners must take action.
For example:
- Check uploaded files in media folders
- Remove unknown or suspicious files
- Ensure server rules block file execution
- Apply temporary security patches






No Comment! Be the first one.