PoC Exploit Released for Apache Syncope Groovy RCE Flaw

A working proof-of-concept (PoC) exploit and full technical details were released for CVE-2025-57738, a high-severity remote code execution (RCE) vulnerability in Apache Syncope, a widely deployed open-source identity management platform used across enterprise and government environments.
The PoC went public on April 20, 2026, roughly three hours after the initial technical write-up by SecureLayer7 researcher yosef0x01.
Apache Syncope Groovy Vulnerability
Tracked as CVE-2025-57738 with a CVSS score of 7.2 (HIGH), the flaw lies in how Apache Syncope handles Groovy-based Implementations. Affected versions include all 2.x builds, 3.x before 3.0.14, and 4.x before 4.0.2.
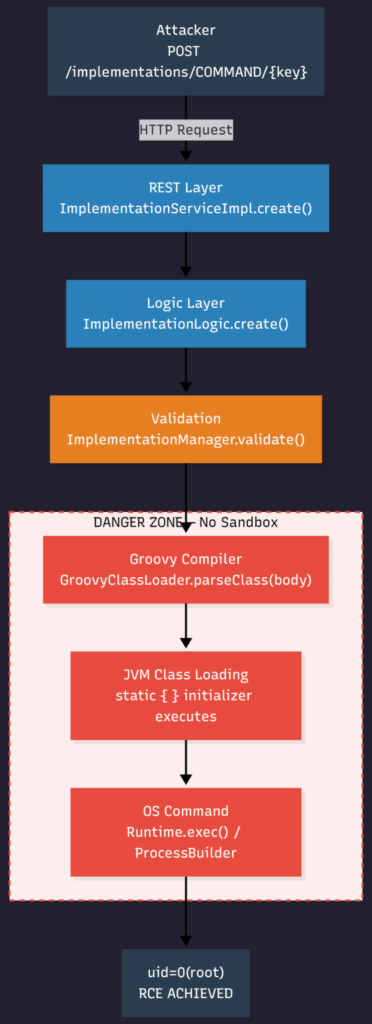
The platform ImplementationManager compiles Groovy code using a bare GroovyClassLoader with no sandbox, no CompilerConfiguration, and no Abstract Syntax Tree (AST) restrictions.
This means an authenticated administrator can upload a malicious Groovy class containing a static { } initializer block code that executes at compile time, before any interface validation occurs.
This grants the attacker unrestricted access to the full JVM API surface, including Runtime.exec(), ProcessBuilder, File, and Socket. In containerized deployments where Syncope runs as root, the impact escalates to full system-level control.
The root cause is classified as CWE-653: Improper Isolation or Compartmentalization, stemming from three compounding failures: the absence of a CompilerConfiguration, unchecked static initializer side effects, and full JVM privilege inheritance.
The published PoC exploit follows a straightforward attack chain:
- The script authenticates to the Syncope REST API using valid admin credentials
- A malicious Groovy payload is crafted and uploaded via
POST /syncope/rest/implementations/COMMAND/{key} - The payload executes during
GroovyClassLoader.parseClass()even if the server ultimately returns an error response - Confirmed exploit output shows
uid=0(root) gid=0(root), demonstrating unrestricted code execution inside the container - An automatic cleanup step removes the uploaded Implementation post-execution, reducing forensic artifacts
Secure Layer7 stated that delegated admin accounts with Implementation management permissions are equally exploitable and that full administrative access is not required. Environments still using default credentials (admin:password) face the highest immediate risk.
Patch and Mitigation
Apache addressed CVE-2025-57738 in Syncope 3.0.14 and 4.0.2 by implementing a multi-layered Groovy sandbox using Jenkins’ Script Security infrastructure.
The fix introduces a SecureASTCustomizer, a SandboxTransformer, and a runtime blocklist blocking dangerous APIs, including ProcessBuilder, Runtime.exec(), File, Socket, and reflection-based methods.
Organizations should take the following actions immediately:
- Upgrade to Syncope 3.0.14 or 4.0.2 without delay
- Audit all delegated admin accounts with Implementation management permissions
- Rotate default credentials and enforce strong authentication policies
- Monitor REST API logs for suspicious
POST /implementations/requests
Apache Syncope has a documented history of similar code-injection vulnerabilities, including CVE-2023-26360 (unauthenticated RCE via Server-Side Template Injection), CVE-2024-27348 (RCE via Apache OFBiz integration), CVE-2024-54676 (privilege escalation via hardcoded AES key), and CVE-2024-52012 (REST API abuse).
The recurring pattern across Syncope’s extensibility layer highlights a systemic need for strict sandboxing wherever user-supplied code is compiled or executed at runtime.






No Comment! Be the first one.