China-Linked GopherWhisper APT Hits Mongolian Government Systems

A previously undocumented China-aligned advanced persistent threat (APT) group has been discovered targeting governmental institutions in Mongolia, deploying a sprawling arsenal of custom malware tools most written in the Go programming language.
Dubbed GopherWhisper by researchers at ESET, the threat actor has been active since at least November 2023 and is believed to have compromised dozens of victims beyond its confirmed targets.
ESET researchers first identified the group in January 2025 after detecting an unknown backdoor later named LaxGopher on a system belonging to a Mongolian governmental entity.
Telemetry data confirmed that approximately 12 systems within the institution were infected, while analysis of attacker-controlled Discord and Slack channels suggested the reach extended to dozens of additional victims.
With no code overlaps to known threat actors and no TTP crossover with documented APT clusters, ESET classified GopherWhisper as an entirely new group. Multiple independent signals supported attribution to China.
Timestamp analysis of recovered Slack and Discord messages revealed that the bulk of operator activity occurred between 8 AM and 5 PM UTC+8, directly aligning with China Standard Time.
ESET researcher Eric Howard noted that the Slack server’s locale metadata was also set to zh-CN, further reinforcing the China nexus.
Multi-Layered and Go-Dominant Toolset
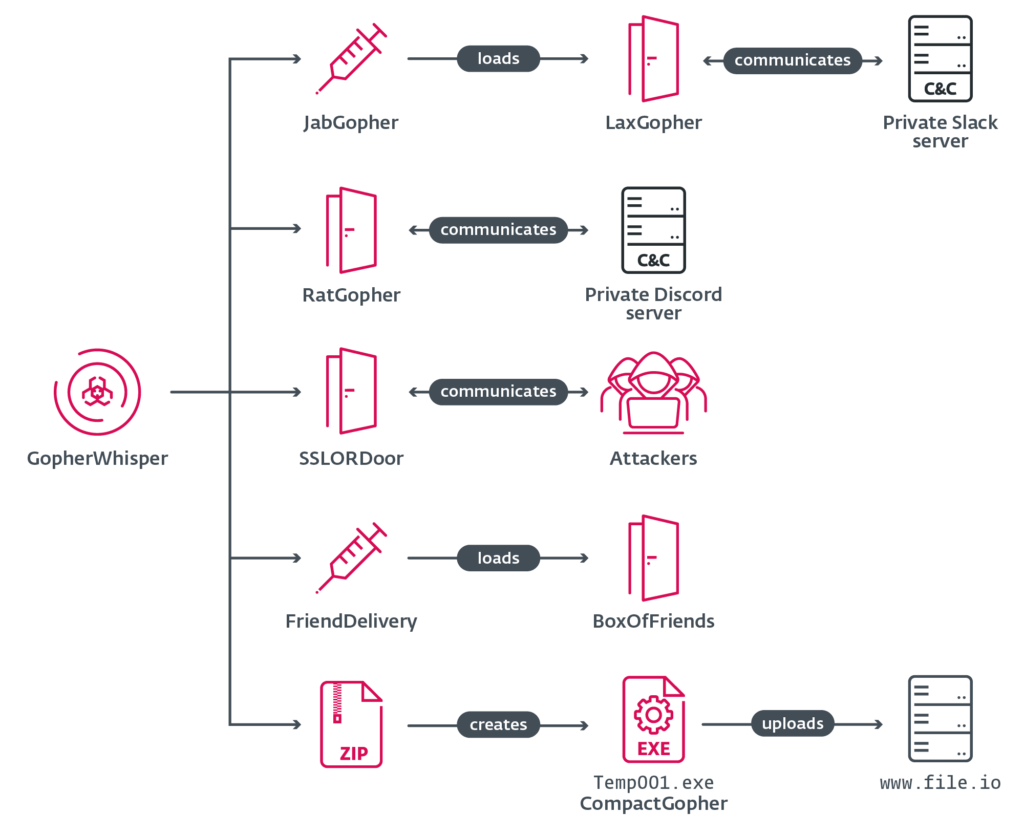
GopherWhisper wields seven distinct malware components across its attack chain:
- JabGopher – An injector that spawns a
svchost.exeprocess and injects LaxGopher — disguised aswhisper.dll— directly into memory - LaxGopher – A Go-based backdoor using a private Slack server for C2, executing commands via
cmd.exeand downloading additional payloads - RatGopher – A Go-based backdoor mirroring LaxGopher but routing all C2 traffic through Discord
- CompactGopher – A Go-based exfiltration tool that filters target file types (
.doc,.pdf,.xls,.pptx), compresses them into ZIP archives, encrypts them with AES-CFB-128, and uploads them to file.io - FriendDelivery – A malicious DLL loader and injector responsible for deploying BoxOfFriends
- BoxOfFriends – A Go-based backdoor leveraging the Microsoft Graph API to create and modify Outlook draft emails for covert C2 communication
- SSLORDoor – A C++ backdoor using OpenSSL BIO over raw sockets on port 443, supporting file read/write/delete operations and drive enumeration.
Hardcoded Credentials Exposed Operations
A critical operational security failure proved invaluable for investigators: the Go-based backdoors contained hardcoded credentials for the attacker’s Slack, Discord, and Microsoft Outlook accounts.
This enabled ESET to recover a total of 6,044 Slack messages dating back to August 21, 2024, and 3,005 Discord messages with the earliest from November 16, 2023.
The recovered C2 traffic exposed operator commands, uploaded files, and development-stage activity, including GitHub repository links referencing Go-based injection and encryption libraries used as development references.
The Microsoft Outlook account tied to BoxOfFriends (barrantaya.1010@outlook[.]com) was created on July 11, 2024, just 11 days before the FriendDelivery loader DLL was compiled, revealing deliberate, staged infrastructure preparation.
Mitigation:
The initial access vector used by GopherWhisper remains unknown, making perimeter hardening more critical. ESET has published a comprehensive set of indicators of compromise (IoCs) in its GitHub repository, including file hashes, domain names, and account identifiers, to help defenders detect and block GopherWhisper activity.
Security teams are advised to monitor for unusual outbound traffic to Slack, Discord, and Microsoft Graph API endpoints, flag DLL sideloading from trusted system binaries like svchost.exe, and audit Microsoft 365 OAuth application permissions for anomalous Graph API access patterns.







No Comment! Be the first one.