NGate Malware Hijacks HandyPay App to Steal NFC Card Data

A new variant of the NGate Android malware family that trojanizes HandyPay, a legitimate NFC relay payment application, to steal contactless payment card data and PINs from victims in Brazil, and the malicious code injected into the app shows strong signs of being AI-generated.
NGate, also tracked as NFSkate, was first publicly documented in August 2024. It works by exploiting a device’s Near Field Communication (NFC) chip to capture and relay contactless payment card data to an attacker-controlled device.
Then they use the data to make unauthorized ATM withdrawals or purchases. Earlier iterations relied on the open-source NFCGate tool to achieve this relay functionality, but threat actors have progressively evolved their techniques with each new campaign cycle.
NGate Malware Hijacks HandyPay App
The shift to HandyPay is primarily financial. Competing NFC relay solutions sold as Malware-as-a-Service (MaaS) on Telegram, such as NFU Pay (~$400/month) and TX-NFC (~$500/month), are significantly more expensive than HandyPay’s optional €9.99/month donation model.
HandyPay, available on Google Play since 2021, natively enables NFC data relay between paired devices, exactly the core functionality threat actors needed, at a fraction of the cost.
Beyond price, the app requires virtually no permissions beyond being set as the default payment application, making the trojanized version far less suspicious to security tools and users alike.
One of the most striking technical findings is the likelihood that the malicious code injected into HandyPay was developed using generative AI (GenAI).
ESET researchers, identified emoji characters embedded within the malware’s debug and toast message logs a pattern highly characteristic of LLM-generated text output.
While definitive proof remains elusive, this aligns with a broader trend in which cybercriminals increasingly leverage AI tools to lower the technical barrier to creating functional malware.
Distribution Vectors and Social Engineering
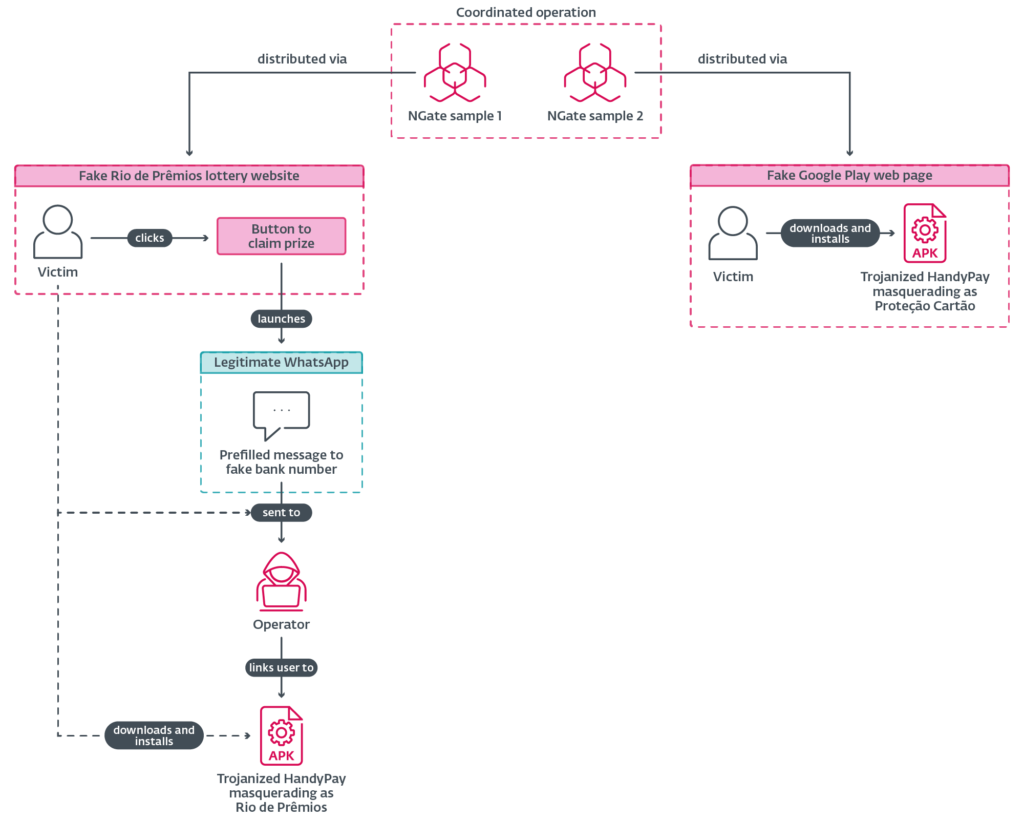
ESET observed two distinct NGate samples, both hosted on the same domain, pointing to a single coordinated threat actor.
The first vector uses a fake website impersonating Rio de Prêmios, a legitimate Rio de Janeiro state lottery.
Victims are tricked into a rigged scratch card game that always “awards” R$20,000, then redirected via WhatsApp to download the malicious APK.
The second vector deploys a fake Google Play page hosting a fake app called “Proteção Cartão” (Card Protection), requiring victims tto sideload the APK manually
Once installed, the trojanized app requests default NFC payment app status, prompts the victim to enter their payment card PIN, and instructs them to tap their physical card to the phone.
The NFC card data is relayed to an attacker’s email address hardcoded within the app. At the same time, the PIN is exfiltrated separately over HTTP to a dedicated C&C server, entirely independent of HandyPay’s infrastructure.
That same C&C server also serves as the APK distribution endpoint, centralizing delivery and data harvesting. ESET found logs from four compromised devices, all geolocated in Brazil, containing captured PINs, IP addresses, and timestamps.
Mitigation
ESET shared findings with Google as an App Defense Alliance partner, and Google Play Protect now automatically detects and blocks known NGate variants.
The HandyPay developer has confirmed an internal investigation is underway. Android users are strongly advised to avoid sideloading APKs, disable NFC when not in use, and keep Play Protect enabled.






No Comment! Be the first one.