Vercel Data Breach: Hackers Claim Full Access to Internal Systems and Source Code

Vercel has disclosed a significant security breach after threat actors gained unauthorized access to internal systems, one of the most widely used frontend cloud platforms powering millions of developer deployments worldwide.
The company published an official security bulletin on April 18–19, 2026, and is actively working with cybersecurity firm Mandiant, while law enforcement has been notified.
The intrusion originated from a compromise of Context.ai, a third-party AI tool used by a Vercel employee. Attackers exploited a malicious or compromised Google Workspace OAuth app linked to Context.ai to hijack the employee’s Google Workspace account.
Once inside, the threat actors pivoted into select Vercel environments and accessed non-sensitive environment variables from a limited number of customer configurations.
Vercel confirmed that environment variables explicitly marked as “sensitive” stored in a way that prevents direct reading showed no evidence of being accessed.
However, any variables that are not marked sensitive but contain secrets such as API keys, tokens, database credentials, or signing keys should be considered potentially compromised and rotated immediately.
The malicious OAuth app has been publicly identified as an indicator of compromise (IOC): 110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com.
Vercel is urging all Google Workspace administrators to immediately audit their environments for this app.
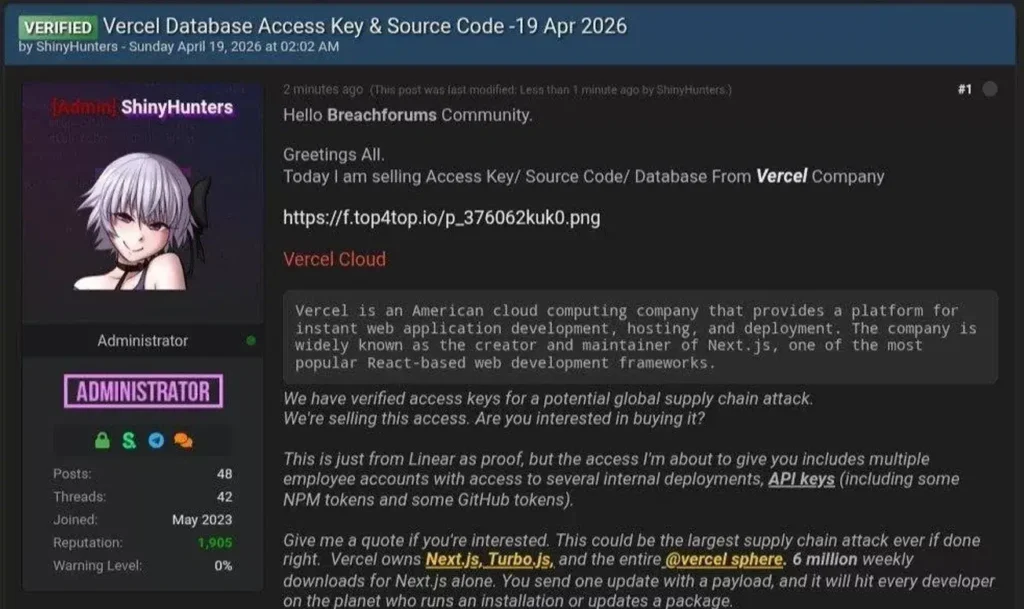
ShinyHunters Claims $2 Million Sale.
The incident drew wider attention after a threat actor claiming to be ShinyHunters posted on BreachForums, advertising alleged access to Vercel’s internal database, source code, employee accounts, API keys, NPM tokens, and GitHub tokens, all for a reported asking price of $2 million.
As proof of access, the attacker shared a text file containing 580 Vercel employee records, including names, email addresses, account status, and activity timestamps, alongside a screenshot of an alleged internal Vercel Enterprise dashboard.
In messages circulated on Telegram, the threat actor also claimed to have been in direct communication with Vercel regarding a ransom demand. However, Vercel has not publicly confirmed any ransom negotiations.
Vercel CEO Guillermo Rauch described the threat actors as “highly sophisticated,” pointing to their operational speed and detailed understanding of Vercel’s internal systems.
Rauch also suggested the attackers may have leveraged AI capabilities to accelerate their intrusion, and strongly urged all customers to rotate API keys and tokens as a precautionary measure.
Vercel confirmed that Next.js and its broader supply chain are unaffected by the incident. All services remain fully operational, and the company has deployed additional protection and monitoring measures across its infrastructure.
Recommended Actions for Vercel Customers
- Rotate all environment variables containing secrets that were not marked as sensitive.
- Enable the sensitive environment variables feature for all future secrets
- Review activity logs in the Vercel dashboard or CLI for suspicious behavior
- Inspect recent deployments for unexpected or unauthorized changes
- Ensure Deployment Protection is set to Standard or higher
- Rotate Deployment Protection bypass tokens if previously configured
- Audit Google Workspace immediately for the identified malicious OAuth app IOC
Customers who have not been directly notified by Vercel currently have no evidence of credential or personal data compromise, though the investigation is still ongoing. Vercel continues to update its official security bulletin as new information becomes available.







No Comment! Be the first one.